Check out our latest blog article: From component to enterprise – modular robotics done right.
75% of IoT Projects Fail. Here’s What You Could Do to Avoid This Scenario
The Internet of Things is a broad term referring to devices and non-electronic objects that produce and exchange data over the Internet. IoT solutions are used across multiple industries, with consumer electronics, retail, and healthcare taking the lead.
Although the Internet of Things could be an $ 11.1 trillion market by 2025 with 41 billion devices deployed globally, today three-quarters of IoT projects fail to deliver on expected value. Thirty percent of those stall at the Proof of Concept stage.
Why do IoT Projects Fail?
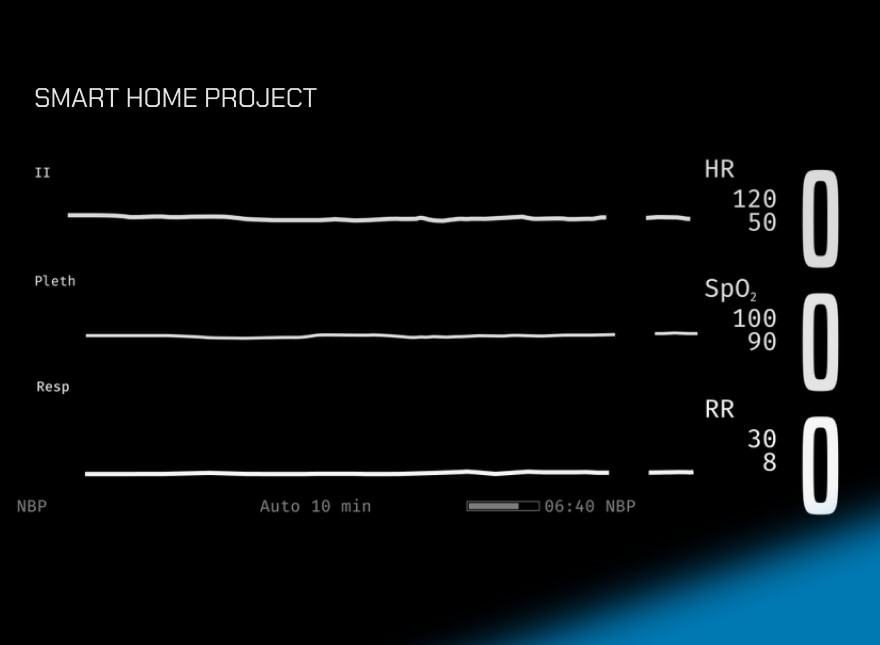
The Internet of Things is a multi-level ecosystem where “things” — i.e., devices equipped with sensors and embedded software — collect miscellaneous data, transfer the data to an on-premise or cloud-based server using secure connectivity protocols, and act on it.
Extra IoT layers include databases and data analytics solutions deployed in the back end, dashboards that visualize historical and real-time sensor readings, and mobile applications, which help users control smart devices and provide anytime, anywhere access to IoT data.
.png?width=1760&name=blog_post_frame_size_880x%20(1).png)
For more information on IoT solution architecture design, download the ITU-T Recommendations document.
Compared to traditional IT solutions like CRM systems and eCommerce websites, the Internet of Things remains a novel concept: 25% of SMBs are still unaware of IoT and its applications in business.
Also, the Internet of Things solutions vary in complexity. A brick-and-mortar store where each item is equipped with a printed RFID tag is an IoT solution, and so is a telecare system that uses wearable devices to track elderly patients’ well-being and location.
According to the Microsoft IoT Signals survey published in 2019, the top challenges companies face when building IoT solutions include:
.png?width=1760&name=blog_post_frame_size_880x_2%20(1).png)
Microsoft claims the lack of technical expertise and resources remains a key barrier to IoT adoption for 50% of the respondents. Meanwhile, the companies that fail to proceed beyond PoC abandon their IoT projects due to high implementation costs and unclear bottom-line benefits.
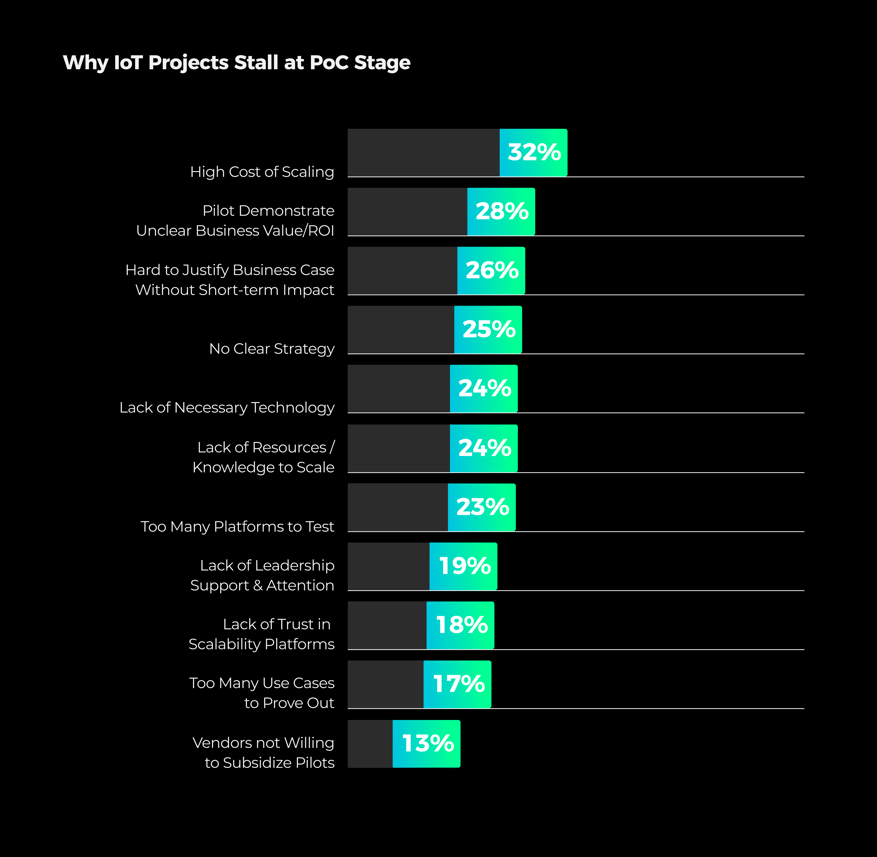
Besides technology limitations, there are intangible aspects that affect IoT project success rates. These include the lack of planning, failure to establish a business case for an IoT solution, and insufficient collaboration between company stakeholders. Notably, 35% of IT executives consider their IoT projects a complete success — compared to just 15% of business executives.
Tips to Overcome IoT Development Challenges
Define IoT Solution Requirements
Before you embark on an IoT development project, there are several questions you need to answer:
- What operations and business processes are you looking to automate with the help of an IoT solution?
- What type of a data capturing device are you going to use?
- Is the gadget capable of running on a proper operating system and processing sensor data locally?
- Where will the data be stored and analyzed?
- What connectivity technologies do you intend to use?
- How are you going to present IoT-generated data to end users?
To verify your idea against business needs, narrow down the project scope, and outline the implementation roadmap, you should start your project with a Discovery Phase.
Download the Softeq Discovery Phase Guide to get started with IoT development.
Together with a skilled Business Analyst, you can define a list of functional requirements for your IoT product and create a preliminary technical vision and project roadmap. Based on the data, it is also possible to provide a ballpark estimate of your IoT solution.
As a next step, it is essential to figure out how the system should function — as opposed to what it’s supposed to do. This is what IT specialists call “non-functional requirements” (NFRs).
The list of common NFRs for an IoT solution includes:
- Availability, fault-tolerance, and disaster recovery
- Scalability and extensibility
- Interoperability and compatibility
- Security and safety
- Industry-specific certification(s) and compliance
The requirements analysis phase will help you choose the optimum IoT development technology stack, plan the solution architecture considering the current and projected workload (i.e., the number of users and connected devices), and get more accurate estimates.
Bear in mind that an IoT project scope is seldom static. Therefore it might be necessary to continue working with a Business Analyst through the project lifecycle.
For example, one of our clients wanted to create a data analytics platform for packaging manufacturers. The company was looking to install temperature and movement sensors on injection molding machines, send the data to a cloud-based server, and analyze the data to prevent equipment failure and fine-tune the manufacturing process. BLE, ZigBee, and Wi-Fi were listed among the preferred connectivity options.
Following the Analysis phase, the project scope was broken down into several iterations:
- The Softeq team created intelligent sensing devices (ISDs) running on custom bare-metal firmware and conducted field tests to make sure the data is produced in a format suitable for Machine Learning-driven analysis
- The findings helped us refine the requirements for the ISDs
- We chose IEEE 802.15.4 as the primary connectivity standard, which serves as a basis for popular connectivity technologies like Bluetooth, ZigBee, and Z-Wave
- We integrated the devices with AWS cloud services to enable data analysis and visualization
The smart approach to project planning and execution helped our customer create a scalable IoT solution and plan their budget accordingly. Failure to define functional and non-functional requirements early on might result in costly reworking later in the development process.
One of our clients, for instance, was looking to build a luxury bracelet with Fitbit-like capabilities. The piece of jewelry was supposed to monitor users’ physical activity, talk to iOS and Android mobile apps via Bluetooth, and send alert notifications to a pre-approved list of contacts in case of an emergency. What the company didn’t realize at the outset was that the bracelet’s metal case would interfere with the Bluetooth signal. To resolve the issue, we had to modify the radio chip and boost the signal strength by 500%.

Focus on Security from Day One
Recent studies show that 46% of US companies that make use of IoT solutions have already experienced at least one security breach, while the cost of an IoT-related cyberattack now amounts to 13.4% of the total revenue for a business with an annual income of $5 million.
What makes the Internet of Things vulnerable to cyberattacks?
- Embedded software that relies on outdated and unsupported operating system (OS) versions
- Poor hardware design that restricts firmware updates
- Insufficient R&D and testing
- Weak password policies
- Lack of universal IoT security standards
- Legacy software systems, which fail to ensure IT infrastructure visibility and detect compromised IoT devices
Software and hardware-level security vulnerabilities allow cybercriminals to intercept sensitive data or harness IoT devices into giant botnets that execute DDoS attacks and may threaten even properly secured enterprise networks. The consequences of large-scale IoT cyberattacks vary from power grid failures to putting patient safety and lives at risk.
Here’s what you could do to avoid IoT security mishaps:
- Encrypt the data stored on a connected device or transmitted between the components of an IoT solution. The use of digital certificates (X.509), TLS cryptographic protocols (SSL, TSL), and reliable connectivity protocols (MQTT, CoAP, AMQP, XMPP, ZeroMQ) helps prevent unauthorized access to sensitive data
- Enhance IoT network security. For this, you should remove outdated connected devices from your corporate network, implement firewalls, and interface your IoT solution with security monitoring tools: AWS IoT Device Defender, Amazon Cognito, IBM IoT Watson Platform, etc.
- Reinforce hardware security. Make sure all sensitive information (personal data, certificates, key, etc.) is encrypted and stored in a secure location, and be sure the device does not install unauthorized firmware updates
Get Your Team on the Same Page
Few companies have the human resources and expertise to create a connected solution under one roof. That’s why businesses often have to outsource the development of their functional IoT components to separate vendors: hardware companies, embedded software specialists, and remote mobile and web development teams. On top of that, there is probably a 3rd party manufacturer responsible for the production of market-ready devices.
When outsourcing IoT development, it is best to choose a company that has been previously engaged in similar projects.
Another case from our portfolio: a manufacturer of lighting products was looking to upgrade their lighting system. The project involved replacing an RF remote control with a BLE-enabled mobile app. The problem was, the firmware and hardware vendors our client hired had never built BLE-controlled devices before. As a result, the app would not connect to the cloud. Another aggravating factor was the platform choice. Google Firebase selected as a primary platform for their IoT mobile and web applications would not work in the location where the firmware development took place, due to local government restrictions.
To make sure your smart solution works as expected, you should appoint a product owner who has both a solid IT background and hands-on experience managing IoT projects — or look for a full-stack IoT company.
More articles on the topic